Israel’s desert hackers fight the dotcom Jihad
We find out how computer boffins on the frontline are fighting to keep Israel and Europe safe from the threat of terror
Deep in the Negev desert, an army of hackers is hard at work. Many European security chiefs are counting on them to develop the tools to prevent further terror attacks in Europe. This mini city of glass and steel is a technology hub surrounded by sand. According to Uzi Zwebner, one of its founders, Gav-Yam Negev, or the Advanced Technologies Park in Beersheva to give it its full title, already houses 1,500 engineers and tech workers. But they’re not making fun smartphone games or designing handy apps.
Because Gav-Yam is a centre for cyber security. Hacking, and hacking prevention, is what this place is all about.
The IDF is in the process of transferring its elite tech units down to Beersheva too. This includes the famous vast Unit8 200, responsible for everything from tracking dubious Facebook posts to allegedly creating the kind of viruses that can dismantle a nuclear reactor.

Nearby, Ben-Gurion University is set to double in size upon the completion of a planned North Campus over the next two decades. Its president, professor Rivka Carmi says: “Cyber technology has now become one of the most sought after research fields, and Ben-Gurion has been declared a hub of cyber technology in Israel by the prime minister.”
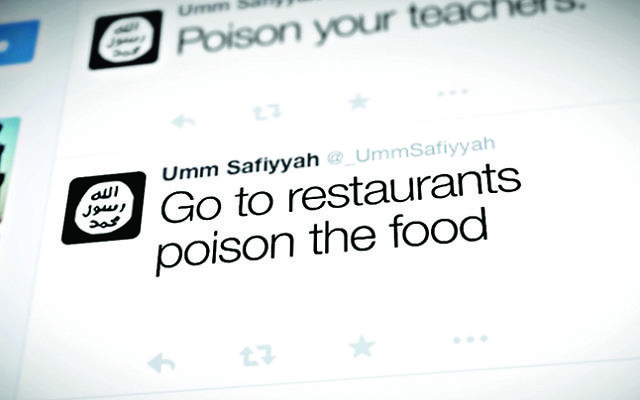
With Europe on high alert for further terror attacks, many European powers are hoping Israeli knowhow can help them spot “lone wolf” jihadi militants. Currently the biggest challenge for Europe’s security services is so-called self-radicalised assailants – terrorists who have been radicalised almost entirely online.
“How do you capture some signs of someone who has no contact with any organisation, is just inspired and started expressing some kind of allegiance? I don’t know. It’s a challenge,” EU counter-terrorism coordinator Gilles de Kerchove admitted at a recent intelligence conference in Tel Aviv.
He said the internet companies have so far refused to monitor their own platforms’ content for material that could be seen as suspicious.
It’s part of a worldwide debate over how much privacy we need and want online – on the one hand, we’d all prefer to keep our banking transactions secret; on the other hand, we want the reassurance of knowing that somebody out there, the police or the security services, can find and stop terrorists before they carry out appalling crimes. Back in March, the debate over whether encryption was a good or a bad thing hit the headlines when the FBI hacked a locked iPhone, possibly with the help of Israeli firm Cellebrite.

“I’m not sure that the FBI had any complication in breaking into the iPhone. I don’t believe in it,” insists Professor Yuval Elovici, director of the Telekom Innovation Laboratories and of the Cybersecurity Research Centre at Ben-Gurion University. “Why did they have to come to a small company in Israel to help them to crack that iPhone? It doesn’t make sense.”
He believes that Islamic State is very sophisticated in its use of technology, presenting a huge challenge for all Western intelligence agencies.
“If somebody is chopping heads, then they’re supposed to be uneducated. This is not the case,” he explains. “[The] people of ISIS are very well educated, many of them have been recruited in western countries. They bring with them a lot of knowledge in technology.
“They are very well exposed to what it is happening in the west from a technological point of view. So there is no contradiction between the fact that they are cruel and the fact that they can employ all the latest technology to do something bad.”
Elovici’s teams of engineers are developing numerous techniques for hacking, including cracking a smart watch to intercept the data
between a computer and wireless printer.
He insists our privacy must not be at the expense of security. “My opinion is that we need to allow the agencies, the national security agencies, to access any information,” he says. “The reason that I am so extreme in my opinion, that I am very, very concerned that these organisations, terrorist organisations like ISIS, will go into acts like biological weapons, chemical weapons, and I am very, very concerned that in the future we may see such terrorist incidents.
“In order to be able to stop such incidents, that even one incident may have a huge impact on our daily life, we need to allow national security agencies access to any information that relates to ISIS.”
With the Gaza border only 25 miles away, turning Beersheva into a cybersecurity hotspot has not been easy – incoming rockets and Israeli bureaucracy have slowed progress. Nevertheless, the army of hackers in the Negev is set to grow to 10,000 in the next five years.

Thank you for helping to make Jewish News the leading source of news and opinion for the UK Jewish community. Today we're asking for your invaluable help to continue putting our community first in everything we do.
For as little as £5 a month you can help sustain the vital work we do in celebrating and standing up for Jewish life in Britain.
Jewish News holds our community together and keeps us connected. Like a synagogue, it’s where people turn to feel part of something bigger. It also proudly shows the rest of Britain the vibrancy and rich culture of modern Jewish life.
You can make a quick and easy one-off or monthly contribution of £5, £10, £20 or any other sum you’re comfortable with.
100% of your donation will help us continue celebrating our community, in all its dynamic diversity...
Engaging
Being a community platform means so much more than producing a newspaper and website. One of our proudest roles is media partnering with our invaluable charities to amplify the outstanding work they do to help us all.
Celebrating
There’s no shortage of oys in the world but Jewish News takes every opportunity to celebrate the joys too, through projects like Night of Heroes, 40 Under 40 and other compelling countdowns that make the community kvell with pride.
Pioneering
In the first collaboration between media outlets from different faiths, Jewish News worked with British Muslim TV and Church Times to produce a list of young activists leading the way on interfaith understanding.
Campaigning
Royal Mail issued a stamp honouring Holocaust hero Sir Nicholas Winton after a Jewish News campaign attracted more than 100,000 backers. Jewish Newsalso produces special editions of the paper highlighting pressing issues including mental health and Holocaust remembrance.
Easy access
In an age when news is readily accessible, Jewish News provides high-quality content free online and offline, removing any financial barriers to connecting people.
Voice of our community to wider society
The Jewish News team regularly appears on TV, radio and on the pages of the national press to comment on stories about the Jewish community. Easy access to the paper on the streets of London also means Jewish News provides an invaluable window into the community for the country at large.
We hope you agree all this is worth preserving.